Enhanced OT Network Monitoring Capabilities Needed to Support Cybersecurity Requirements
Better asset inventories and rapid threat detection should be sufficient justification for industrial companies to invest in continuous OT network monitoring. But product assessments should also consider future developments such as IT/OT cybersecurity convergence, external security support and digital transformation.
Continuous operational technology (OT) network monitoring has become an essential part of every industrial/OT cybersecurity strategy. It provides the asset and connectivity information users need to build strong defenses. It also alerts users when rules are violated. These benefits are enough to justify investments in this technology, but product evaluations should also consider how products support future needs. Three major developments are changing OT cybersecurity requirements. Increased CISO involvement and IT/OT cybersecurity convergence require greater visibility of OT assets and vulnerabilities. The use of external service providers such as security operations centers (SOC) and third-party managed security service providers (MSSP) requires greater integration of OT and IT cybersecurity tools. Digital transformation initiatives expand the number and type of assets that need to be monitored.
Continuous OT network monitoring is the enabler for every cybersecurity maturity step. Asset discovery and inventory capabilities provide the starting point for actions taken at the Secure level. Advances in Defense and Coverage require a deep understanding of data flows within and around the system. The ability to compare current network traffic to a baseline based on past traffic is the essence of anomaly detection, which is additional protection.
While there are some differences, all leading OT network monitoring solutions can support the basic OT visibility and anomaly detection needs of facility cybersecurity teams. But industry developments are rapidly changing the requirements for an effective solution. Choosing a vendor that understands and addresses these emerging needs is essential.
Nozomi Networks Solves the Problem

Nozomi Networks is a leading provider of continuous OT network monitoring solutions. Organizations around the world use the Guardian platform to protect their critical infrastructure. Nozomi’s comprehensive product set reflects its extensive experience in continuous OT network monitoring and understanding of evolving market needs.
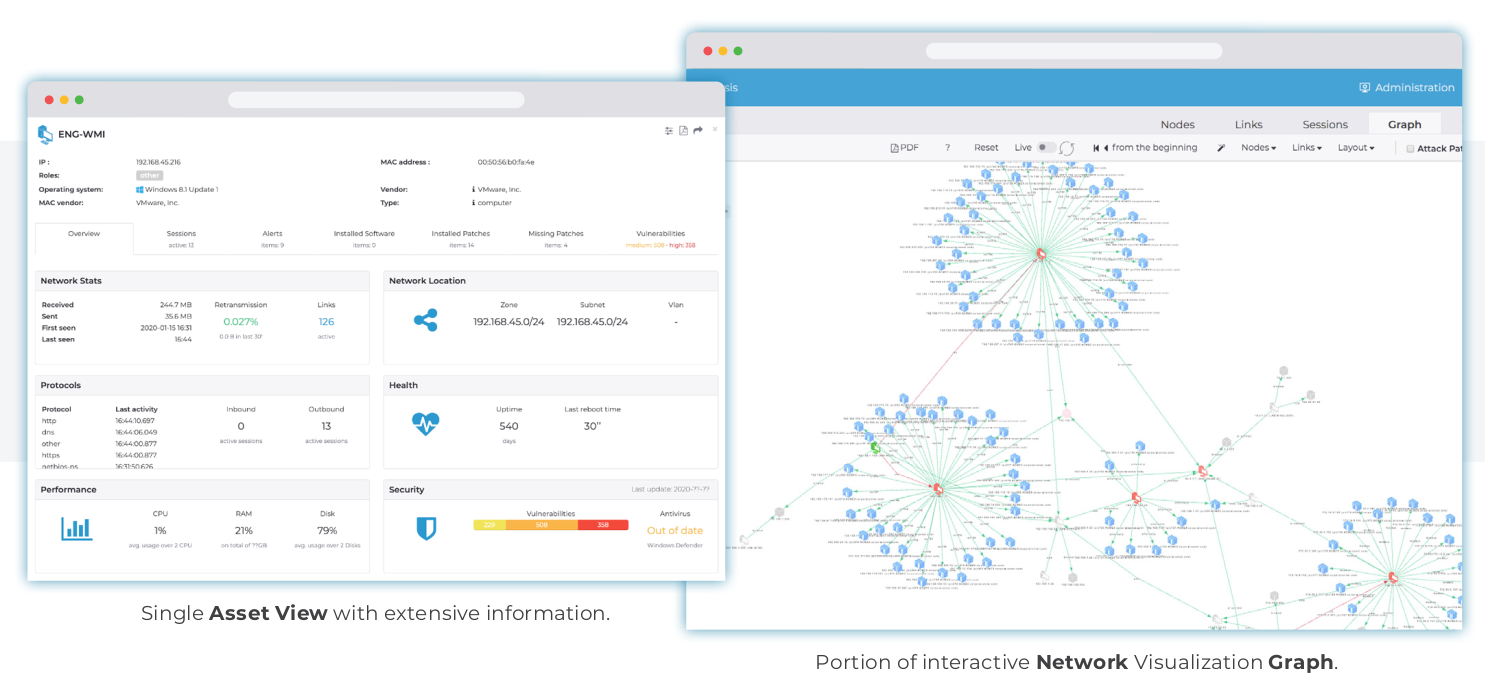
Guardian performs network monitoring activities. It includes functions for reading network packets, DPI, presence discovery, threat detection, and anomaly detection. This product also supports local users with network visualization, vulnerability assessment, risk monitoring and security reporting. Guardian supports a wide range of industrial protocols. The product also supports the use of threat information from the company’s OT ThreatFeed subscription service to increase detection of known threats.

Integration has been a key focus of Nozomi Networks’ development efforts. Nozomi has developed interfaces for a wide range of OT products, network devices, SIEMs, popular IT security management tools and access control products, and Guardian has an open API for data sharing with external applications.
You can contact us for detailed information about Nozomi Networks products and other cyber security products.